Issue: Users receive errors USERTrust Legacy Secure Server CA is malformed or invalid. IE users may receive error: “Information you exchange with this site cannot be viewed or changed by others. However, there is a problem with the site’s security certificate“.
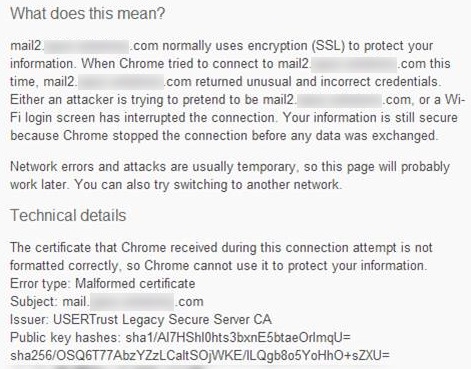
Example of USERTrust malformed certificate error in Chrome connecting to OWA:
Cause: The USERTrust intermediate cert issued by Comodo references an Entrust.net root cert that does not meet the new 2048-bit requirements.
Ramifications:
- As of March 11th 2014, the non-compliant 1024-bit Entrust.net root cert has been removed from the Microsoft Root program
- The 1024-bit Entrust root will be removed from Mozilla Firefox version 28 scheduled for release on March 18th
- Google Chrome will display warnings and/or block content using the 1024-bit Entrust Root cert
Resolution: Obtain an updated intermediate certificate from your certificate authority (Comodo or other) and replace the intermediate cert on your Web server with the new intermediate cert.
Link to download the new Comodo intermediate cert: https://support.comodo.com/index.php?dload=Download&_m=downloads&_a=downloadfile&downloaditemid=94
Instructions to import an intermediate certificate in IIS
Testing: The best way to test whether the end-user connection is using the new 2048-bit Entrust root is to check the certificate path using IE
Update 3-13: In some cases the only way to get it so the client receives the new intermediate certificate is to have Comodo re-issue the SSL cert and and re-install it on your server.
Note: re-issuing a certificate requires similar procedures as renewing or requesting a certificate. Instructions for renewing a certificate on Exchange 2003 IIS 6
Instructions for renewing a certificate on Exchange 2013
Update 3-14:
In some cases, in order to resolve this issue for affected users, the Comodo intermediate certificate needs to be replaced on the end user desktop Intermediate Certificate Store. This can be accomplished via:
- pushing out the new intermediate cert to all users via Group Policy or other deployment mechanism
- one-by-one on each desktop by following these instructions to import an intermediate certificate, but don’t forget to delete the existing Comodo USERTrust intermediate certificate.